Identity and the CIS Framework
In cybersecurity, control frameworks can be tremendously helpful in either building a security program from scratch or improving an existing one. The Center for Internet Security (CIS) control framework has grown in popularity, as it takes most of the guesswork out of program assessment and design.
Unlike other control frameworks, CIS is mostly prescriptive. It leaves less to be interpreted than other programs like NIST. That said, every organization has its own elements of the business that are most important to protect. So, even after choosing to follow CIS, you may find that there are control areas you want to cover immediately and others you’ll want to put off until your next budget cycle.
Identity Security in CIS
Identity Security is most important for modern organizations already on a pure cloud IT deployment or legacy organizations beginning to support the ability to work from anywhere via Hybrid IT stacks. If you’ve chosen to follow the CIS control framework, you might be struggling with what features to look for in an identity security solution.
To help eliminate some of these questions, we’ve done the legwork by leveraging our own research and the expertise of some of our CISO partners who have hands-on experience using the CIS framework.
The following sections will describe certain product and feature categories offered by modern identity security solutions and show you how they map to specific controls in the CIS framework. We’ve provided some additional commentary in the next section to help clarify how these are relevant to each CIS control. If you’re only interested in seeing a direct CIS control mapping, feel free to jump straight to our CIS Mapping Matrix (Navigate to the end of this post).
Inventory
All successful security programs start with taking stock, so it shouldn’t be a surprise that there's an inventory requirement in almost every core section of the CIS framework. These include Device inventories, Network inventories, Application inventories, and so on.
Following this model, identity-related inventories are also required. That said, this part can get a little confusing. There are 3 specific controls that mention identity-related inventories. There are as follows:
5.1: Establish and Maintain an Inventory of Accounts
5.5: Establish and Maintain an Inventory of Service Accounts
6.6: Establish and Maintain an Inventory of Authentication & Authorization Systems
Here’s where a good identity security solution will help. It will inventory your user and administrator accounts and keep track of service accounts, as they’re primarily stored in IAM tools but not always called out separately.
Furthermore, as some organizations have more than just one identity system, keeping track of multiple Authentication and Authorization systems is required. For example, it’s quite common for an organization to have both Google Workspace with its in-built IdP functions and Okta as a purpose-driven IdP. This can extend to other providers in the space, including EntraID, Ping, etc., and the in-built IdPs that are part of cloud environments like AWS, Azure, or GCP.
Account Exposure
One of the ways an Identity Security platform is most helpful is in performing both simple and complex queries of the data in your IdP to surface accounts or configurations that need to be addressed. Since each account can be configured differently, these configuration vulnerabilities can remain hidden with no obvious indication that they should be addressed.
The following CIS controls align well to reports that are common in an identity security platform.
5.3: Disable Dormant Accounts: Dormant accounts can be found by accessing a ‘dormant accounts’ report. If your organization uses a specific number of days as a benchmark to consider them dormant, you can easily add that to a filter (45 days in the case of CIS 5.3).
5.4: Restrict Administrator Privileges to Dedicated Administrator Accounts: Again, a report will be provided showing you the accounts on which this has not been done so it can be properly fixed.
6.3: Require MFA for Externally Exposed Applications: An identity Security solution may only give you a part of the picture. Most identity security platforms can tell you whether a secure MFA is being used. However, if you have externally exposed applications that live outside the SSO, a direct integration needs to be done to monitor this anywhere else.
6.4: Require MFA for Remote Network Access: If a VPN is used for accessing your network remotely, and that VPN is connected via SSO, you’re all set. Otherwise, you may need to check if your identity security provider supports integration with the MFA provider you use specifically for VPN or any other remote access techniques you’re using.
6.5: Require MFA for Administrative Access: Since Administrative Access can mean many things, this one can be tricky. However, an Identity Security platform can certainly help ensure that any SSO-joined Administrative access is protected by MFA.
Centralized Control & Visibility
There are a number of tools that support Access Management functions. As mentioned in the Inventory section above, You might have AWS, Google Workspace, Azure, and EntraID all embedded in different places in your organization. If each of these is supported by your identity security provider, it can be a huge help in managing your identity deployments centrally. Without this, you’ll never get the centralized control and visibility described here in CIS control 5.6
5.6: Centralize account management through a directory or identity service
While we believe that Control 5.6's intended purpose is to enforce the use of an SSO, it’s possible that your organization may have multiple SSOs that are not synchronized. In this case, further centralization via an Identity Security platform is warranted.
Logs: Suspicious Behavior & Forensics
Many would look to a SIEM for logging. However, SIEMs can be incredibly expensive and provide minimalistic value in real-time detection and response. Many of the customers we speak to would prefer to go without a SIEM but still feel the need for logging that keeps track of access and authorization.
In the CIS framework, there are many logging requirements. Some may be in relation specifically to DNS logs, Command Line logs, Web Request URL Logs, and more. Depending on the nature of your business, you may or may not have a closed on-premise network where all of these logs exist.
If you run a hybrid or full cloud IT stack instead, collecting and retaining authentication and authorization logs and events is incredibly important. The following controls apply.
8.1: Establish and Maintain an Audit Log Management Process. Again, if the focus of your audit log storage is Access Management related, an Identity Security platform will help store and manage these logs.
8.2: Collect Audit Logs: Collection in this case is as simple as setting up an integration and ensuring that you set your retention rules.
8.3: Ensure Adequate Audit Log Storage: Log storage is typically included in the cost of your Identity Security platform subscription. One thing to watch out for here is that SSO platforms often do not come with any form of long-term storage, limiting storage to 7 or 30 days, depending on whether you use Okta, EntraID, Ping, etc.
8.4: Standardize Time Synchronization: This, too, is something that is standardized by an Identity Security platform.
8.10: Retain Audit Logs (90 days minimum): Most Identity Security platforms will allow for a minimum of 1 year of data retention.
8.11: Conduct Audit Log Reviews (weekly or more): Audit log reviews are difficult and time-consuming. The goal here is to review audit logs for suspicious activity. An identity security solution is primarily designed to do this for you, giving you specific reports and alerts that surface suspicious activity. Without one, the process is incredibly manual and unlikely to happen weekly.
8.12: Collect Service Provider Logs (authentication and authorization events): In this case, CIS is referring to 3rd party and Cloud Service Provider logs. This can be a more difficult source of logs to store if you have not included any Cloud SaaS Applications in your SSO. Direct integrations may be available, though given the extreme number of SaaS applications on the market today, your best option is to focus on integrating these tools with your SSO for access.
Influencing User Behavior
This section consists of several CIS sub-controls that originate from different control sections. However, each of these sub-controls has a common theme, as they all pertain to user behavior.
The world of Identity Security is synonymous with user behavior in many ways. Since there are multiple ways in which an identity security solution can help influence user behavior, we’ve grouped these items together and will cover how a solution can help.
9.1: Ensure Use of Only Fully Supported Browsers and Email Clients: This may be easy to cover if your organization only supports connecting to company resources with a managed device. That said, most modern organizations offer BYOD or may not have device management or EDR solutions in place. This can massively open you up to the choices of your employees, at which point you’ll see browsers like Opera or Vivaldi connecting to corporate systems. A good Identity Security solution watches for anomalous browser use as a part of its anomaly detection and will allow you to set up a workflow informing the user that a certain browser was detected on their account, which is not supported by the company. While blocking these browsers is much more difficult, this inform & track method will dramatically help you cut down on unsupported browsers.
14.2: Train workforce members to recognize social engineering attacks: Ideal training should include real-world experience. A good identity security solution will incorporate end-user communications to help analysts understand the hard-to-answer question during investigations: Was this you? By doing so, employees learn the results of their accidental clicks or other potential missteps so that real-world scenarios are used in employee education.
14.3: Train workforce members on authentication best practices AND 5.2: Use Unique Passwords
Authentication is wrought with behavioral challenges. Employees may not be using a password manager or strong authentication, but short of forcing them to do so, which is generally unrealistic, the only option is to let them know how and why they can help. When brute force attacks are detected, there is a perfect opportunity to inform an employees that they need to be sure they are using a password manager, a unique password, or a strong MFA. An identity Security platform can help by automating these powerful messages so that employees know that their account is under attack and they’re motivated to act securely.
Conclusion
As organizations continue to progress toward a more cloud-centric IT stack, few solutions see the majority of workforce activity—the view of device & network solutions continues to fragment. Identity has generally become the one true center of all workforce behavior, so we wouldn’t be surprised to see more and more identity-focused requirements appear in frameworks like CIS.
If there’s anything in this guide that you’d like to review in greater detail, our engineering and product teams love to get into these details. Otherwise, we hope this overview was helpful in understanding more about how Identity Security is core to the CIS framework.
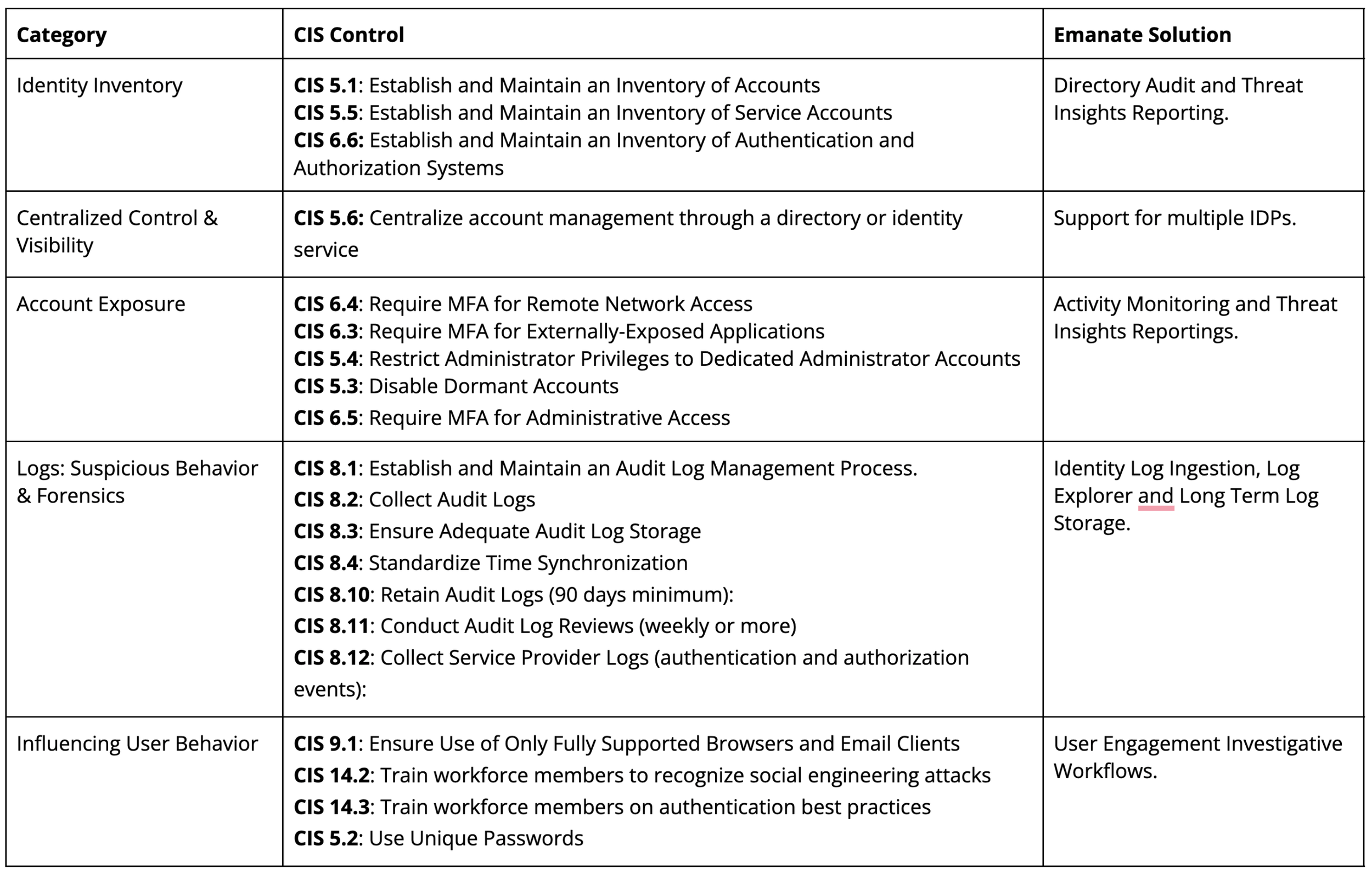
CIS Framework Mapping
As always, if you’re ever interested in a more detailed conversation with our Engineers or Identity Experts, don’t hesitate to Contact Us.